Just before a court hearing schedule for Tuesday, the FBI decided to pursue and attack method that would not require Apple’s assistance. This effectively put the FBI’s case on pause, and created an anti-climactic end to the battle between the government and the tech giant over hacking into the San Bernardino shooters iPhone. A U.S. District Court in California ruled that good cause had been shown by the government for the delay and ordered it to file a status report with the court on April 5.
Originally the FBI had wanted Apple to write software that would change the amount of password attempts that could be made before the phone erased itself. Currently, an iPhone will be erased after 10 unsuccessful attempts with the wrong passcode. The FBI stated that it would need Apple’s help to get around this hurdle, but apparently that has changed. This leave many to wonder how to agency might defeat the phone’s security.
“You can always attack the phone while it’s running. There are hundreds of people in the world, if not more, who can do that,” said Rod Schultz, vice president of product at Rubicon Labs.”They can attach a debugger to the device, and modify the instructions that are doing the policy check,” he told TechNewsWorld.
The password also could be recovered through a technique known as NAND mirroring. It requires making a copy of the iPhone’s memory. Then, after 10 wrong password guesses erased the phone’s contents, the memory would be reloaded into the phone and the FBI could take 10 more tries at cracking it. That process would be repeated several times until the FBI was able to hack into the phone. The downside is that it takes a long time, and that is most why the FBI didn’t want to do it.
The is some skepticism about the reasons why the FBI asked for the delay. “Those of us who are watching both the technology arguments and the legal arguments are somewhat skeptical of the claim that the FBI suddenly discovered they could get into the phone,” said Mike Godwin, general counsel and director of innovation policy at the R Street Institute.
“The legal arguments that Apple produced were quite strong,” Godwin told TechNewsWorld. “I think the FBI was worried it was going to lose based on the legal arguments.”
As for Apple, its public stance is that the issue must be settled outside the courts. “Tim Cook has never said Apple will never cooperate with the FBI,” observed R Street’s Godwin.
Article via TechNewsWorld, 23 March 2016
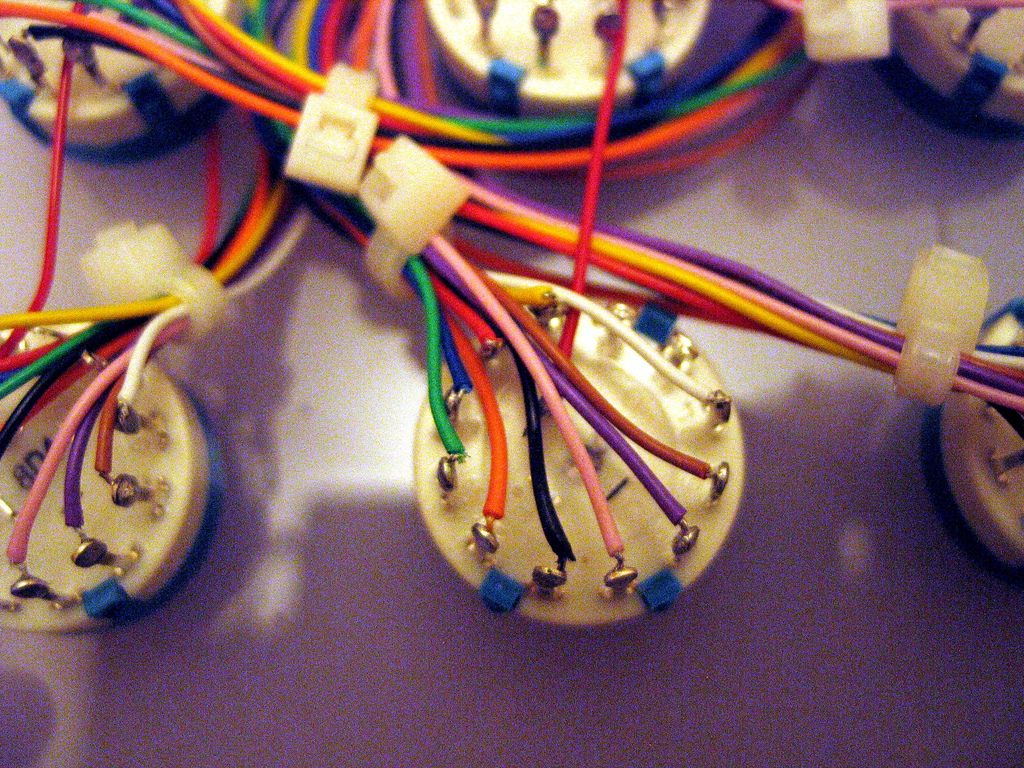
Photo: The Apple – FBI Electronic Encryption Fight RGB Triptych v1.3 by Surian Soosay [Creative Commons Attribution-NonCommercial-NoDerivs]